Phishing attacks can come from unexpected sources. For instance, fake spam phone calls and emails are common methods for phishers who try to use scare tactics or incentives to get you to reveal sensitive data like credit card information. Cyber criminals use current political and worldwide events to their advantage by creating a sense of urgency and fear.
It is important to be able to recognize a phishing attack to protect yourself against identity theft. These attacks typically occur through email, phone calls, or malicious websites to solicit personal information by posing as a trustworthy organization or federal agency.
Avoid falling victim to identity theft or data loss by reviewing these safety tips:
- Check the website in the URL address bar. When browsing the Internet, look for the lock icon and "https://" in the web address bar to ensure that your information is protected. The "s" indicates website encryption is enabled to protect your information.
- Be wary of calls or texts that request confidential information. Banks and government agencies will not ask you to reveal personal information over the phone.
- Review all received emails. Only open emails and attachments from people you trust. Hover your cursor over the website link in the email to identify the true destination link. Access websites by typing the website address directly into the URL bar instead of clicking the website link in the email.
- Phishers use scare tactics. If you are pressured to provide sensitive information, initiate contact with the requestor, e.g., your doctor or bank, directly to confirm the authenticity of the request.
- Install and keep your anti-virus up-to-date. Before adventuring on the web, ensure an anti-virus is enabled and that you’re running the latest version. This can prevent malware from wreaking havoc on your device and preventing future data theft.
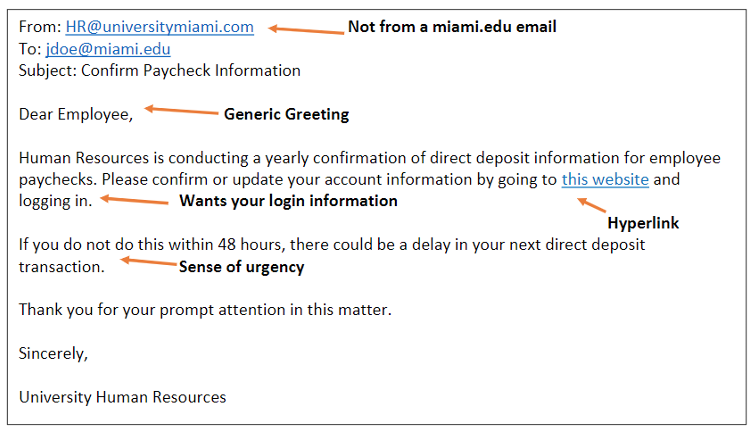
How to spot a phishing email:
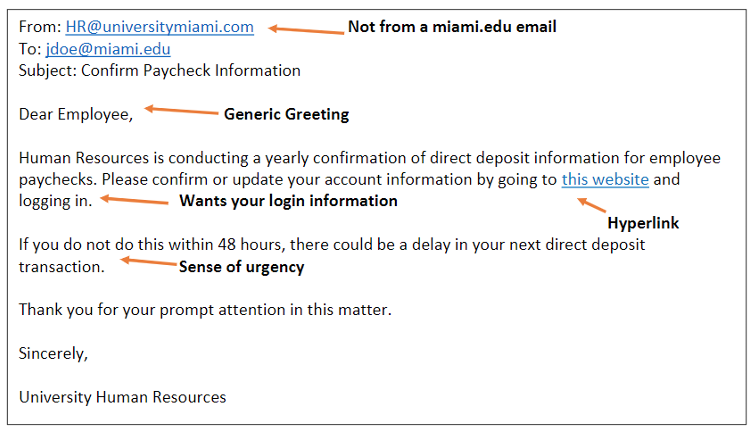
- Asks for protected information. Reputable organizations will never ask for protected information via email, phone, or text message. Always be suspicious if this occurs.
- A generic greeting. Legitimate companies will begin an email with your first and last name. Phishing emails often address the user with "Dear Member" or "Dear Bank Customer" because the sender does not know your name.
- Uses a fake email address. The sender's email address looks legitimate at first glance, but is found to be fake when examined more closely. For example, jdoe@miami.edu versus jdoe@umiami.com. Sometimes the return email address is not a valid email address at all.
- Creates a sense of urgency or fear. The email generates a sense of desperation by using time-sensitive ploys such as claiming that your account may have been compromised, and you should click this link to change your password immediately.
- Poor spelling and grammar. A phishing email from a non-legitimate source may spell words incorrectly throughout, or have grammar mistakes.
- Poor formatting or design. Strange breaks between words or fuzzy company logos are indicators of a possible scam.
- Hyperlinks or attachments. These emails generally encourage you to click on a hyperlink, which then directs you to a malicious website or installs malware onto your computer. Try hovering your mouse over the link. Does the URL link match what is in the text? Does the actual link look like it belongs to whomever sent the message? The email may also ask you to download an attachment, for example, while masquerading as a work colleague asking you to look over a document. Downloading files from unverified sources is one of the main methods of malware distribution—think before you click!
If you suspect a message to be a phishing attempt, you can quickly report it using Outlook's "Report Message" feature. If you are not using Outlook or the feature is not available, you can forward the phishing email (as an attachment) to phish@miami.edu.
If you are victim of phishing, e.g., you clicked a link and/or downloaded an attachment from a suspicious source, please contact the IT Service Desk, as well as the Information Security Office (ISO) at: infosec@miami.edu.
Have questions? We're here to help!
If you have questions about cybersecurity, or if you want to learn more about how to stay safe online, contact the Information Security Office (ISO) at: infosec@miami.edu